


Replace Static AWS Credentials with Ephemeral Access
Enforce Just-in-Time ephemeral permissions across AWS environments.
Request a demo
Most AWS environments rely on standing permissions that persist long after tasks are complete. Ensure static access can't be exploited by permanently eliminating long-lived credentials with ephemeral, time-bound access.
Enhance Security & Scalability Challenges in AWS
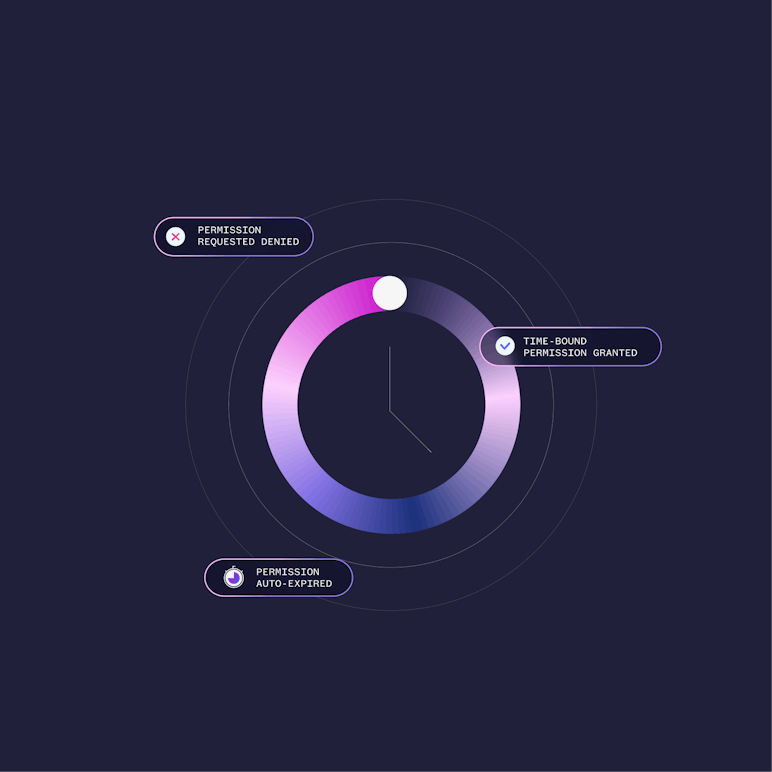
Just-in-Time Access
Automatically grant and revoke just-in-time (JIT) permissions for agentic, human and non-human identities.
Achieve Zero Standing Privileges
Enforce and achieve true ZSP by eliminating all standing privileges across your AWS environments.
Access Resources and Applications
Centralize management of identity privileges and entitlements for AWS resources via UI or CLI for workflow flexibility.
Secrets Governance
Automatic granting of ephemeral, time-bound secrets while managing static secrets in a secure vault.
Proactive Monitoring
Analyze access changes and policy drift, identify risk or unusual behavior, and support post-incident investigation.



How Britive Eliminates Static Access Risk in AWS
Watch how a Fortune 500 financial services company used Britive to enable ephemeral access and enhance security for 5000+ users.
Watch the VideoWatch the Video
Explore Ephemeral AWS Access
Ready to eliminate the risk of standing access across your AWS environment? Get in touch with our team of experts today.



FAQ
What makes Britive different from a traditional PAM solution?
Britive is purpose-built for cloud environments, unlike legacy PAM tools designed for on-prem data centers, or other agent and proxy-based PAM platforms.
Can Britive integrate with ___?
Yes! Britive is API-first and integration-friendly, allowing seamless out-of-the-box integrations with cloud infrastructure providers (AWS, GCP, Azure, etc.), SSO & Identity Providers (Okta, Microsoft Entra ID / Azure AD, Ping Identity), SIEM & Logging Tools (Splunk, Datadog, etc.) and DevOps & CI/CD Pipelines (Terraform, GitHub Actions, Kubernetes, etc.).
You can find a starting list of our integrations here.
How long does it take to implement Britive?
Britive can be fully deployed in a matter of hours or days with our agentless and proxyless design to minimize the number of configuration changes needed.
Does Britive allow the import of privileged accounts for other systems?
Yes, Britive offers the ability to import privileged accounts from other systems for seamless integration and centralized management. Privileged accounts from cloud platforms like AWS, Azure, and Google Cloud, as well as on-premises systems, can be imported into Britive. Automated discovery simplifies the process, identifying existing accounts for streamlined integration.
Does the Britive solution offer any "break glass" access?
Yes, Britive offers "break glass" access capabilities, including support for managing emergency access to critical accounts such as AWS root accounts. This ensures operational continuity and secure access during emergencies. This includes strict access policies, logging, and enforcement of strong authentication methods for enhanced security.
Break glass access is also strictly monitored and governed by approval workflows, ensuring that usage is authorized and fully auditable.
Does Britive support session recording?
Yes, Britive's session recording capability is lightweight and easy to deploy for selective monitoring of RDP and SSH sessions.
Case studies
Britive in the Real World
001
002
003
001
002
003



Financial Services Company Streamlines Access Management
Forbes Saves Costs & Removes Standing Privileges to Align with Zero Trust Security
Fortune 500 Retail Giant Eliminates Standing Access Across Growing Cloud Footprint
4000+
54k+
67k+
10,000+
400+
< 30 min
Privileged human identities managed
Static Privileges Eliminated
Static privileges eliminated across all cloud providers
Non-human identities access managed
Identity profiles managed in GCP
Total on and off-boarding time, reduced from 3 days






