


Ephemeral JIT Access = ZERO standing access risk
JIT access is everywhere.
True ephemeral JIT access is Britive.
Request a demo
Traditional JIT:
A permanent admin role is created ahead of time, stored in a vault, and temporarily unlocked. The role remains in place even when it is not being used.
Britive's Ephemeral JIT:
Privilege is created at request time using native cloud APIs, without sitting in the data path, and removed automatically when the task ends. Nothing exists before the request, and nothing remains after.
Why Ephemeral JIT Scales, Lowers Cost, Eliminates Risk
Built to Scale
• No agents or proxies to deploy per system
• No vault infrastructure to size or maintain
• New environments inherit policy automatically
Lower Cost by Design
Less infrastructure, less overhead:
• Fewer tools and less infrastructure to run
• Less operational overhead for access management
• Smaller audit effort with session-level records
Risk Reduced at the Privilege Layer
• No standing privilege in the environment
• No credentials left behind between sessions
• Smaller blast radius by default



How Britive Eliminates Static Access Risk
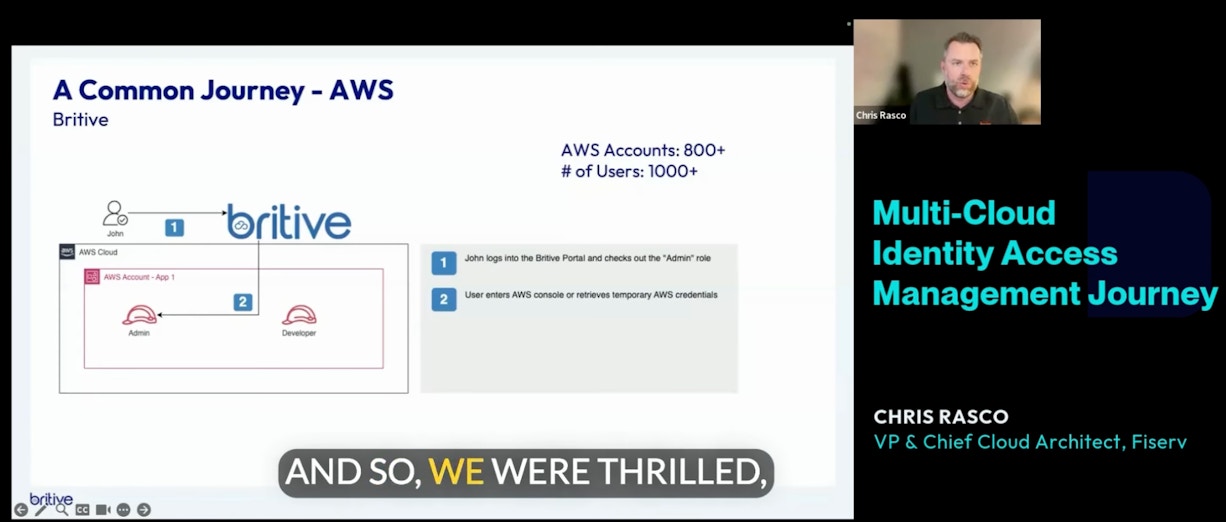
Discover how a Fortune 500 financial services company, used Britive to operationalize JIT in AWS and enhance security for thousands of users.
Watch the VideoWatch the Video
Enterprise-Scale Ephemeral JIT in 3 Steps

1. Request Access
Access is requested through the tools your teams already use.
Slack. Teams. ServiceNow. CLI.

2. Privilege Created
That same policy is evaluated in real time.
A short-lived privilege is minted for the task, using the same policy across environments.

3. Privilege Removed
When the task ends, access is removed automatically.
No manual revocation. No credential rotation.
The policy cleans up after itself.
Britive’s Ephemeral JIT is enforced wherever standing access creates risk.
Across environments
• Cloud, hybrid, and on-prem environments
• SaaS and business-critical applications
Across workflows
• Kubernetes and cloud-native platforms
• CI/CD pipelines and automation workflows
Across identities
• Human and machine identities
• Agentic AI and autonomous workloads
REQUEST A DEMOREQUEST A DEMO
Stop Renting Keys. Start Removing Privilege.
Book a demo to see how we eliminate standing access at enterprise scale.



FAQ
What do you mean by “ephemeral JIT access”?
Ephemeral JIT means the privilege itself does not exist until it is requested. Access is created at runtime, scoped to the task, and removed when the task ends. Nothing stands by before or after.
How is this different from traditional JIT access?
Traditional JIT limits when a credential can be used. The privileged role still exists. Britive limits when privilege exists. If the work is not happening, the privilege is not there.
How does this work with Agentic AI and autonomous workflows?
Agentic AI needs access that is dynamic, task-scoped, and short-lived. Britive treats AI agents as first-class identities and applies the same access model used for humans and automation. Privilege is created at runtime for a specific action, scoped by policy, and removed immediately after. Agents never hold standing access or long-lived credentials, even as they act autonomously.
Does this work for machine identities and automation?
Yes. The same access model and policies apply to pipelines, service accounts, and automated workflows.
Can Britive integrate with ___?
Yes! Britive is API-first and integration-friendly, allowing seamless out-of-the-box integrations with cloud infrastructure providers (AWS, GCP, Azure, etc.), SSO & Identity Providers (Okta, Microsoft Entra ID / Azure AD, Ping Identity), SIEM & Logging Tools (Splunk, Datadog, etc.) and DevOps & CI/CD Pipelines (Terraform, GitHub Actions, Kubernetes, etc.).
You can find a starting list of our integrations here.
Does Britive allow the import of privileged accounts for other systems?
Yes, Britive offers the ability to import privileged accounts from other systems for seamless integration and centralized management. Privileged accounts from cloud platforms like AWS, Azure, and Google Cloud, as well as on-premises systems, can be imported into Britive. Automated discovery simplifies the process, identifying existing accounts for streamlined integration.
Does the Britive solution offer any "break glass" access?
Yes, Britive offers "break glass" access capabilities, including support for managing emergency access to critical accounts such as AWS root accounts. This ensures operational continuity and secure access during emergencies. This includes strict access policies, logging, and enforcement of strong authentication methods for enhanced security.
Break glass access is also strictly monitored and governed by approval workflows, ensuring that usage is authorized and fully auditable.
Does Britive support session recording?
Yes, Britive's session recording capability is lightweight and easy to deploy for selective monitoring of RDP and SSH sessions.
Do I still need a vault?
Britive offers vaults where static secrets are unavoidable. For cloud and SaaS privileged access, Britive issues ephemeral privileges directly and does not depend on stored admin credentials.
What about audits and compliance?
Every request, decision, and expiration is logged. You can see who had access, to what, and for how long without reconstruction.
Case studies
Britive in the Real World
001
002
003
001
002
003



Financial Services Company Streamlines Access Management
Forbes Saves Costs & Removes Standing Privileges to Align with Zero Trust Security
Fortune 500 Retail Giant Eliminates Standing Access Across Growing Cloud Footprint
7000+
54k+
67k+
30,000+
400+
< 30 min
Privileged human identities managed
Static Privileges Eliminated
Static privileges eliminated across all cloud providers
Non-human identities access managed
Identity profiles managed in GCP
Total on and off-boarding time, reduced from 3 days






