Audits & Compliance Regulations in the Cloud
For enterprises in the cloud, privileged user audits can be a source of fear and frustration.
Why?
The most common reason is that audits discover abnormalities, errors, and in some cases, malicious behavior. Turning up these things, in and of itself, is beneficial. It provides insight and helps keep workloads and data safe. However, it can also force enterprises to admit mistakes and suffer costly disruptions and compliance violations.
90% of enterprises have two or more cloud infrastructure providers (AWS, Azure, GCP, etc.) and more than 40 other critical cloud services. Despite tangible business benefits, multi-cloud presents challenges for security and audit teams when it comes to controlling privileged access and meeting compliance regulations.
Meeting regulatory compliance requirements is critical to an enterprise’s success. Enforcing least privilege access (LPA) for all users – human and service IDs – cross-cloud is the pivotal first step. Unfortunately, service IDs are often ignored during audits; excessive permissions are considered a problem only when an enterprise’s blind spot is pointed out, or they suffer a breach or disruption.
What’s more, as the number of users within public cloud environments grows, maintaining compliance for various industries becomes more difficult. After all, when thousands of users are granted thousands of permissions to access workloads that contain sensitive data, auditors have their hands full.
It is imperative, therefore, for auditors to ask challenging questions, to probe deeper regarding which users have access to what data. Only through visibility and vigilance can enterprises know if privileged users are using permissions actively and appropriately.
That’s why enterprises need a privileged access management (PAM) solution that covers all major cloud providers and empowers auditors to maintain secure environments.
Enterprises that do not enforce LPA put security at risk and can incur serious compliance violation fees. Today’s cloud data breaches are often the result of excessive, unused, and misconfigured permissions. In many cases, uncovering these errors falls to auditors.
Unchecked, bad actors can target privileged users and find ways to exploit excessive or unused permissions to infiltrate an enterprise’s environment. Cloud breaches cost enterprises more than $4 million on average. Consequently, cybersecurity regulations are tightening, and financial penalties are becoming more severe.
The good news is that multi-cloud LPA is very much an attainable goal – even for large enterprises. When LPA is enforced as a policy across your cloud environments for every user, it is more likely that you will meet compliance regulations and protect workloads and data. Granting minimum permissions reduces risk and minimizes your attack surface. It aligns with the principle of Zero Trust security; in fact, without LPA enforcement, maintaining a policy of Zero Trust is out of reach.
Here, we are talking about two sides of the same coin. From a policy perspective, enterprises should adhere to LPA. From an auditing perspective, privileged users must actively use the permissions they have, and use them only for strict, policy-driven objectives. Absent this, enterprises are at risk.
If there is a single concept that regulatory bodies, industry frameworks, and cloud providers agree on, it’s least privilege access. Seven well-known frameworks emphasize the critical nature of LPA:
Regulatory Frameworks that Require Least Privilege
1. SWIFT Customer Security Controls Framework. Financial institutions in the Society of Worldwide Interbank Financial Telecommunication (SWIFT):
“When you create IAM policies, follow the standard security advice of granting least privilege, or granting only the permissions required to perform a task. Determine what users (and roles) need to do, and then craft policies that allow them to perform only those tasks.”
2. Payment Card Industry Data Security Standard (PCI DSS). Per PCI DSS Requirement 7:
“Restrict access to cardholder data by business need-to-know to ensure critical data can only be accessed by authorized personnel, systems and processes must be in place to limit access based on need to know and according to job responsibilities. Need to know is when access rights are granted to only the least amount of data and privileges needed to perform a job. Access rights are granted to only the least amount of data and privileges needed to perform a job.”
3. National Institute of Standards and Technology (NIST) Framework for Improving Critical Infrastructure Cybersecurity. NIST PR.AC-4:
“Access permissions and authorizations are managed, incorporating the principles of least privilege and separation of duties.”
4. American Institute of Certified Public Accountants’ SOC for Cybersecurity:
“The entity authorizes, modifies, or removes access to data, software, functions, and other protected information assets based on roles, responsibilities, or the system design and changes, giving consideration to the concepts of least privilege and segregation of duties, to meet the entity’s objectives.”
5. Health Insurance Portability and Accountability Act (HIPAA):
“The Privacy Rule generally requires covered entities to take reasonable steps to limit the use or disclosure of, and requests for, protected health information to the minimum necessary to accomplish the intended purpose. The implementation specifications for this provision require a covered entity to develop and implement policies and procedures appropriate for its own organization, reflecting the entity’s business practices and workforce.”
6. General Data Protection Regulation (GDPR):
“The controller shall implement appropriate technical and organizational measures for ensuring that, by default, only personal data which are necessary for each specific purpose of the processing are processed. That obligation applies to the amount of personal data collected, the extent of their processing, the period of their storage and their accessibility. 3In particular, such measures shall ensure that by default personal data are not made accessible without the individual’s intervention to an indefinite number of natural persons.”
7. California Consumer Privacy Act (CCPA). The CCPA specifies in Section 11 that:
“Any consumer whose non-encrypted and non-redacted personal information, as defined in subparagraph (A) of paragraph (1) of subdivision (d) of Section 1798.81.5, is subject to an unauthorized access and exfiltration, theft, or disclosure as a result of the business’s violation of the duty to implement and maintain reasonable security procedures and practices appropriate to the nature of the information to protect the personal information may institute a civil action …”
The First Cloud-Native Solution
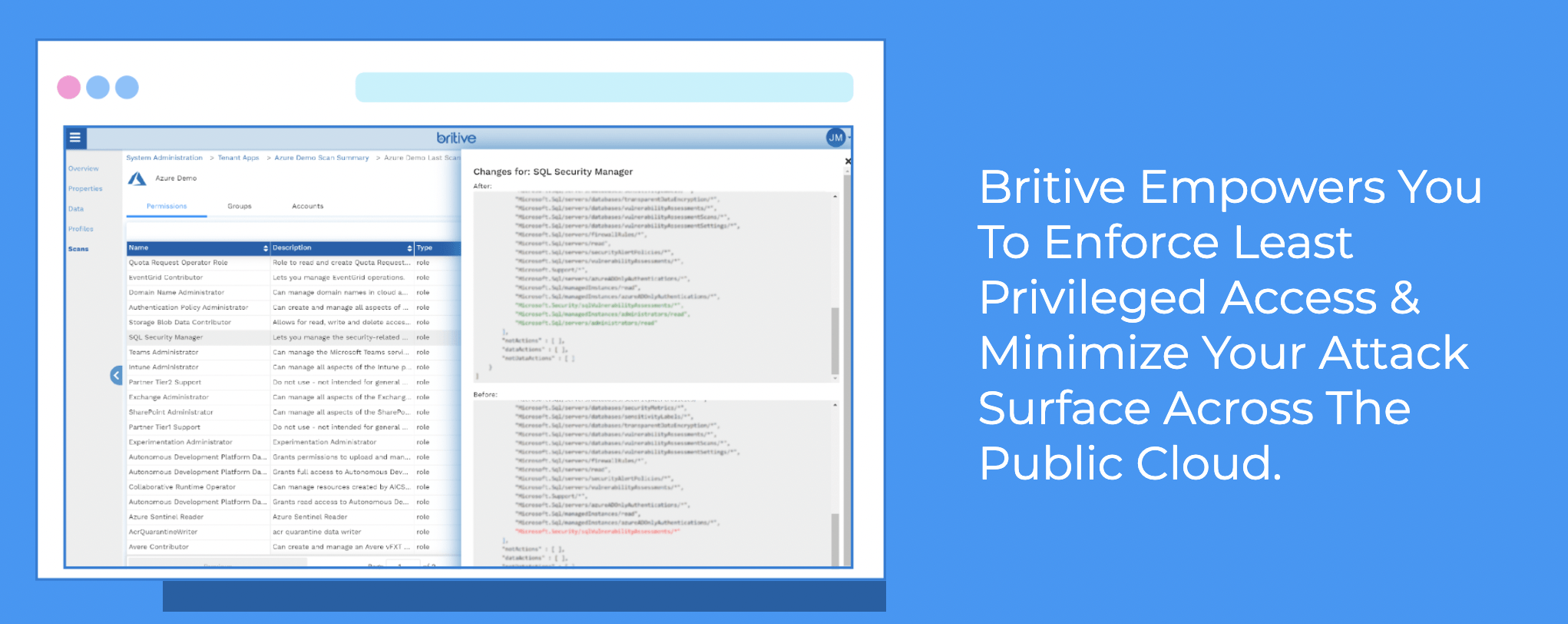
The Britive Multi-Cloud Privilege Management Platform gives auditors, admins, SecOps, and DevOps the tools they need to achieve business goals securely, quickly, and still meet compliance regulations.
Our Just-In-Time (JIT) permissioning model – along with role right-sizing, advanced visibility, and powerful auditing capabilities – lets you control privileges proactively. Excessive permissions granted to thousands of users is no longer an unsolvable problem. With Britive, it can be a thing of the past.
The takeaway is clear: enterprises that wait for an audit or a breach to identify privileged user misconfigurations operate under elevated levels of risk. To prevent a costly mistake or attack, enforce a policy of LPA and give auditors the tools they need to gain visibility and management cross-cloud.

