Two new reports from Gartner highlight the need for organizations to adopt Cloud Infrastructure Entitlements Management (CIEM) and improve the protection of keys and secrets related to managing the digital identities for a growing number of devices and workloads.
The first report, titled, “Emerging Technologies and Trends Impact Radar: Security,” tracks the technologies driving innovation in the security market. These include cross-cloud visibility, advanced analytics, CIEM, and others.
Widespread use of cloud service providers (CSPs) such as AWS, Azure, GCP, Salesforce, and Oracle is the impetus behind implementing security technologies that are better suited to cloud environments. One challenge organizations face is moving beyond legacy security controls and deploying cloud-native solutions designed to support SecOps and DevOps teams.
Regardless of where an organization is on its cloud journey – whether you are still on-prem, hybrid, or cloud-forward – it’s imperative to clearly understand the cloud landscape and recognize the controls needed to chart a fast path to a digital future.
CIEM & Cloud-Delivered Analytics
Gartner recommends investing strongly in cloud-delivered analytics. Organizations know analytics are essential but often struggle with collating and comprehending the data in usable ways. But when it comes to managing users in the cloud and, especially, multi-cloud environments, taking advantage of the visibility analytics provide is critical. Only when admins can extrapolate human and machine behavior can they effectively manage privileges and roles.
Gartner cites Britive as an industry leader in the CIEM quadrant. CIEM is fast becoming a key component of security management as organizations grow more dynamic and mature in the use of various CSPs.
Entitlements in multi-cloud environments tend to be granular and inconsistently defined. CIEM pushes through the problem so organizations can manage cloud access via time-managed controls like Just-In-Time (JIT) permissions. While many CIEM solutions offer time control permissions for Azure and AWS, having JIT for all key cloud providers – including GCP – is ideal.
CIEM detects anomalies in account entitlements and provides enforcement and remediation capabilities. Enforcing zero-trust policies via a least privilege access model is the overarching objective, and Gartner rightly states that an important “use case for CIEM offerings is a graphical visualization of access rights and entitlements across multi-cloud environments. This allows organizations to get a granular view of entitlements associated with a particular identity.”
IAM Planning Guide
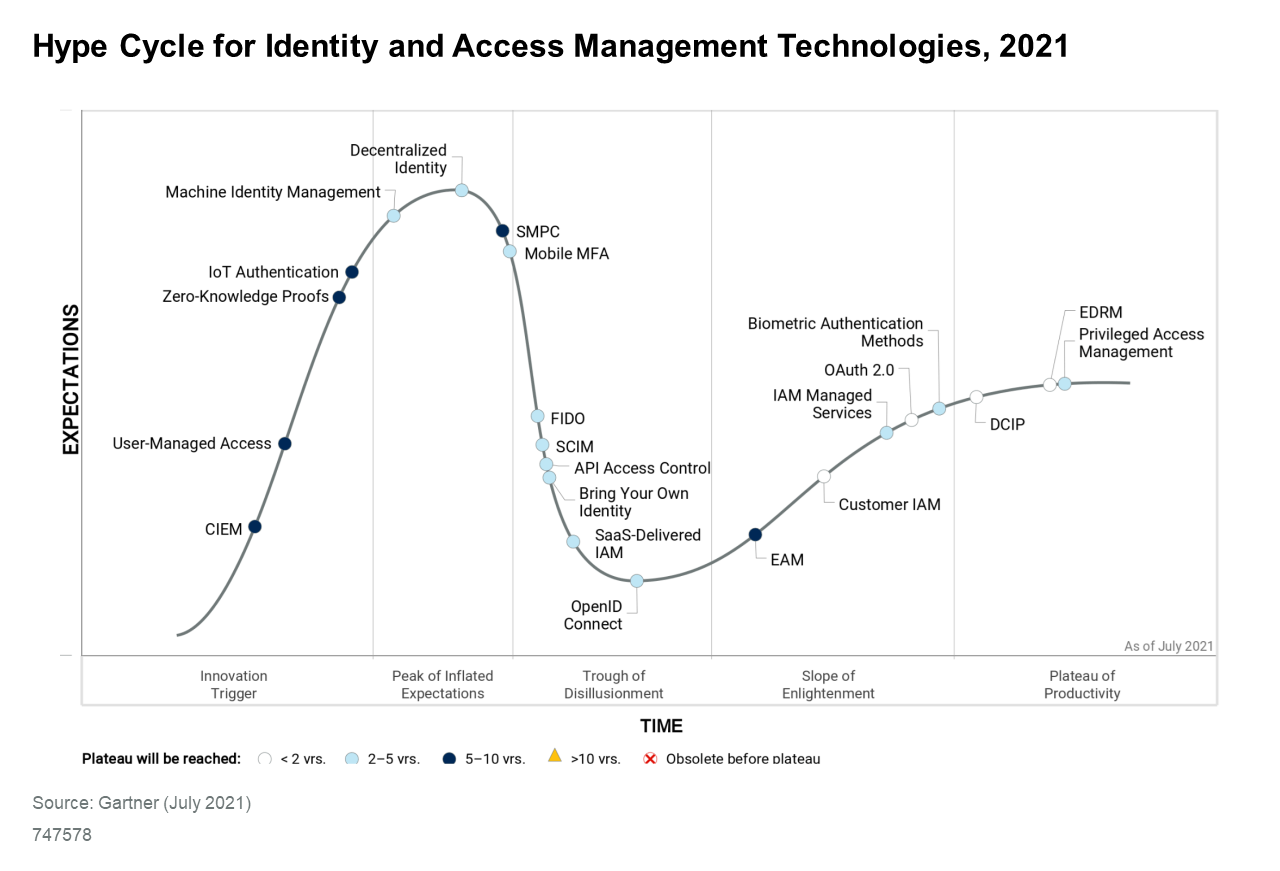
The second recent Gartner report, titled, “2022 Planning Guide for Identity and Access Management,” focuses on why it’s necessary to improve the protection of digital keys and secrets in cloud environments. This is particularly true for managing the growing number of machine IDs operating in today’s workplace.
Devices and workloads that are accessed using keys and secrets need higher levels of attention if organizations want to maintain security and full functionality cross-cloud.
What does that look like?
Gartner recommends hardening software and integration pipelines by “adopting machine identity management disciplines and configuring security controls” DevOps organizations use.
Secrets governance lets builders work quickly and securely by automatically granting and expiring privileges. As a result, users and machine IDs can check out of role-based elevated privilege profiles for specific cloud services, either for the duration of a session or task, for a set amount of time, or until the users check the profile back in manually.
Secrets can also address the issue of account sharing, which is becoming increasingly common with the growing use of cloud resources within DevOps organizations, by automating shared secret rotation invoked via policy.
Lastly, organizations can investigate who has access to which secrets. In the event of a security incident, you need to tie secrets back to identities for proactive monitoring and post-incident investigation. Uncovering exploited identities or individuals, access changes, policy drift, and risky activities results in superior mitigation.
Gartner’s 2022 planning guide for IAM is an essential read for cloud-forward organizations that recognize the need for cloud-native security and management controls.
If we all agree that identity is the new perimeter, it’s time to secure every human and machine user across an organization’s cloud environment.
• Download Gartner’s 2022 Planning Guide for Identity and Access Management
• Download Gartner’s Emerging Technologies and Trends Impact Radar: Security

